Proxy Servers: things you need to know
A proxy server is a device that acts as a connection or an intermediary between users and the internet. It adds an extra protection to the device. How? When an internet request is sent, it is routed to the proxy, which then receives the response from the web server and sends the data from the page to the computer’s browser, such as Chrome, Safari, or Microsoft Edge. As a result, it helps keep cyber intruders out of a private network. Proxy servers can be configured to act as web filters, shielding your computer from internet risks such as viruses. This added security is also useful when used in conjunction with a secure web and a secure network.
Proxy sites
Proxy sites are sometimes used for personal reasons, such as concealing location online or accessing banned content on the Internet. However, they can be used to achieve various vital functions in businesses such as: boosting security, protecting employees’ online work, avoiding crashes, and controlling websites the employees have access to…. It improves overall network performance, protects data from illegal access, and maintains anonymity.

How to Obtain a Proxy?
Proxies exist as either Hardware or Software. What is the difference? Hardware proxies connect your network to the internet, where they receive, send, and forward data. Whereas software proxies are an application developed by someone, where user should download and install it on his computer to be able to use the proxy. A software proxy usually needs a monthly subscription, few are free.
Free proxy servers provide fewer addresses and cover a few devices, whereas proxies with subscription can fulfill the needs of a corporation with numerous devices.
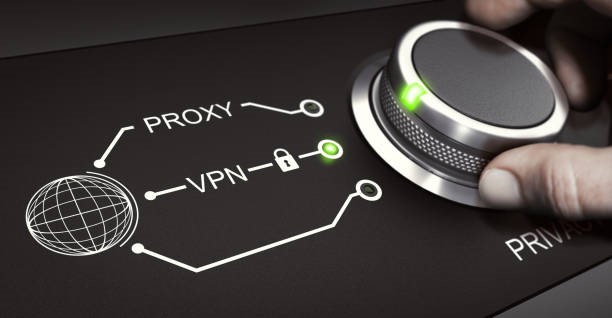
How Does the Proxy Protect Computer Data and Privacy?
Before understanding how does a proxy work, we should explain why we need a proxy. In fact, proxies are used for many reasons, but the main one is to hide or change the IP address when browsing a website in order to protect the sensitive data and the private information of a user. We should know that to be able to access the device (Internet, personal data, application, files…), an IP address is needed, and no one can access the user data if he has a different IP address. What is the relation between proxy servers, IP address, and device security? In fact, hackers can only get access to the proxy’s IP address which is different from the device’s IP address .The process starts by checking the data that enters and exits your computer or network and applying restrictions to prevent the exposure of digital addresses.

Geonode proxy
Geonode proxy or residential proxies is one of the most cost effective proxy networks. It handles around 2 million different IP addresses across over 140 countries. Geonode’s proxy servers are intended to protect copyrights that becomes a serious worry in this digital especially when it comes to brand protection which is a critical issue for businesses. How do Geonode’s proxy works? It simply locate and flag pirated content for the responsible to take appropriate measures (block the website, penalties…).Also, Geonode offers the feature of Ad verification allowing publishers to ensure that their ads are being shown in the right place and to the right people.
Proxy SwitchyOmega is a free proxy, compatible with Chrome and Firefox. Its importance is in making simple and fast for the user to change the proxy settings in your browser. They can also instruct Auto Switch to automatically utilize the correct proxy for the correct website. In addition to the user’s ability to open specific websites via specific proxies. Using Omega Proxy is a completely secure process, where they certify that no data are shared with third parties without the approval of the user, and data are only utilized for concerns related to the proxy’s operation.
In conclusion, we can notice that proxy servers on large networks help to increase reliability by filtering dangerous data. Also, they allow users to preserve their web content and detect or stop any stealing process. So it is very important to understand how the proxy server works and its importance in the security field online.